Difference between revisions of ":DNA BiWeekly Meeting5"
(Created page with "=DNA Tech Support Meeting= ==Meeting Information== Participant Code: 104-357-739-22 Participant URL: https://join.shoretel.com/conference/10435773922 Dial-in Info: +19179427...") |
(→Method 3) |
||
| (8 intermediate revisions by the same user not shown) | |||
| Line 14: | Line 14: | ||
*Salesforce | *Salesforce | ||
==3rd Party Camera Training== | ==3rd Party Camera Training== | ||
| + | ===Target=== | ||
| + | [[file:CrapCam1.jpg|200px]] [[file:CrapCam2.jpg|500px]] | ||
| + | ===Toolkit=== | ||
| + | *NMap or Angry IP Scanner | ||
| + | *ConfigTool | ||
| + | *Dahua Recorder | ||
| + | ===Unknown=== | ||
| + | *P2P only? | ||
| + | *Web Interface? | ||
| + | *DHCP or Static by default | ||
| + | *HTTP Port | ||
| + | *TCP or UDP Port | ||
| + | *ONVIF Compatability | ||
| + | *ONVIF Port | ||
| + | *ONVIF Credentials | ||
| + | ===Known Intel=== | ||
| + | *User name and password | ||
| + | ===Methods of Locating Device=== | ||
| + | ====Method 1==== | ||
| + | *The easiest method of locating an IP camera on the network would be to use a Dahua recorder, and try to locate the device under, "Registration" | ||
| + | [[file:CrapCamLocate1.jpg|800px]] | ||
| + | |||
| + | From this above image, we can see that the camera is on an IP address of 192.168.2.108. We can also see that the HTTP port is, "8080" | ||
| + | |||
| + | With this information we can attempt to login to the camera via http://192.168.2.108 or http://192.168.2.108:8080 | ||
| + | |||
| + | ====Method 2==== | ||
| + | *ONVIF Device Manager is another method we can use to locate the device. Be sure to input the user name and password at the top of this application before attempting to locate the device on the network. You can also use ONVIF Device Manager to verify the ONVIF credentials to the target device. This might be different than the credentials to login via the web interface. | ||
| + | |||
| + | [[file:CrapCamLocate2.jpg|800px]] | ||
| + | |||
| + | ====Method 3==== | ||
| + | *The last method to locate a device on the network is to use NMap. This tool will scan the network, and locate and devices. Be sure to use, "Ping Scan" and input the range of IP addresses that you wish to search for into the tool. Example: 192.168.2.1-255 will scan all IP addresses starting at "192.168.2.1" to "192.168.2.255" and all IP addresses in between. You can also use this tool to determine which ports the device is broadcasting on currently. | ||
| + | |||
| + | [[file:CrapCamLocate3.jpg|600px]] | ||
Latest revision as of 18:33, 7 February 2018
Contents
DNA Tech Support Meeting
Meeting Information
Participant Code: 104-357-739-22
Participant URL: https://join.shoretel.com/conference/10435773922
Dial-in Info: +19179427142
Additional Calling Info: Canada Dial in +1 (647) 558-3006
Topics
- 3rd Party VMS
- 3rd Party Cameras
- Shoretel
- Salesforce
3rd Party Camera Training
Target
Toolkit
- NMap or Angry IP Scanner
- ConfigTool
- Dahua Recorder
Unknown
- P2P only?
- Web Interface?
- DHCP or Static by default
- HTTP Port
- TCP or UDP Port
- ONVIF Compatability
- ONVIF Port
- ONVIF Credentials
Known Intel
- User name and password
Methods of Locating Device
Method 1
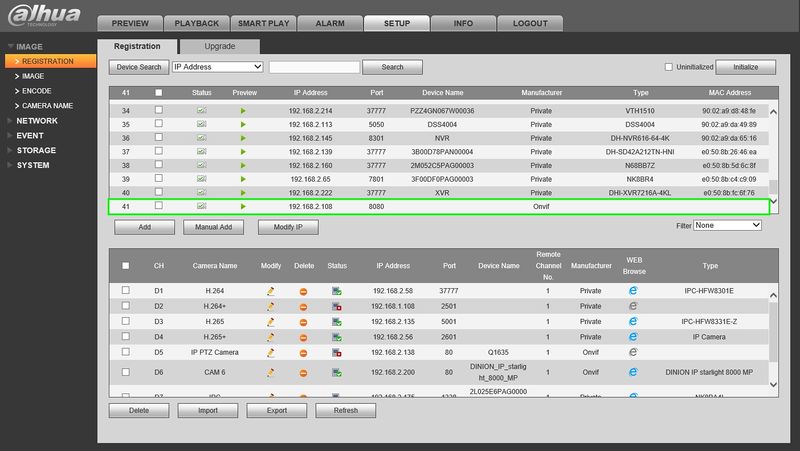
- The easiest method of locating an IP camera on the network would be to use a Dahua recorder, and try to locate the device under, "Registration"
From this above image, we can see that the camera is on an IP address of 192.168.2.108. We can also see that the HTTP port is, "8080"
With this information we can attempt to login to the camera via http://192.168.2.108 or http://192.168.2.108:8080
Method 2
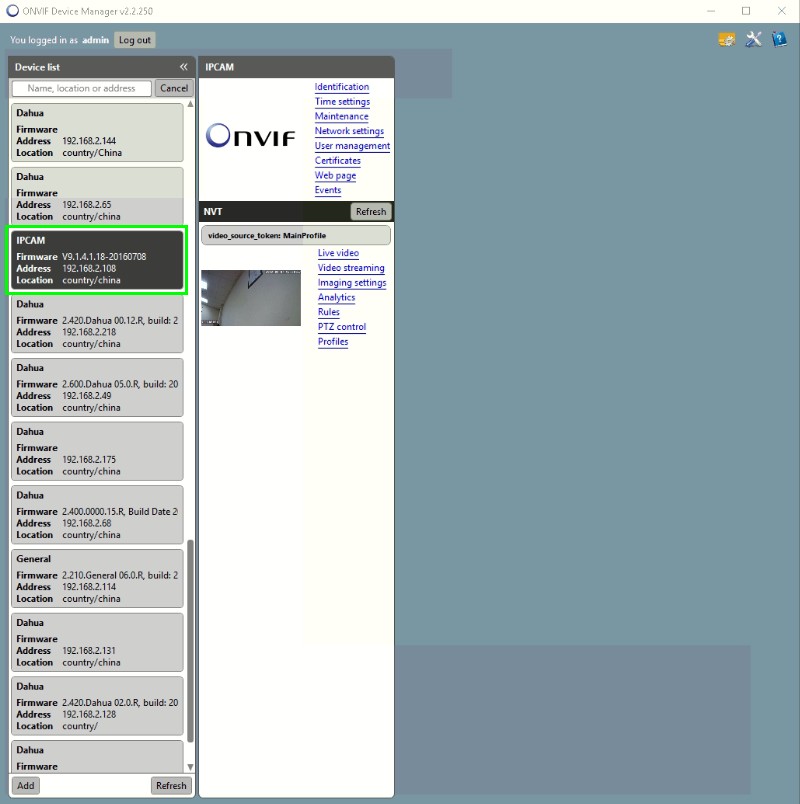
- ONVIF Device Manager is another method we can use to locate the device. Be sure to input the user name and password at the top of this application before attempting to locate the device on the network. You can also use ONVIF Device Manager to verify the ONVIF credentials to the target device. This might be different than the credentials to login via the web interface.
Method 3
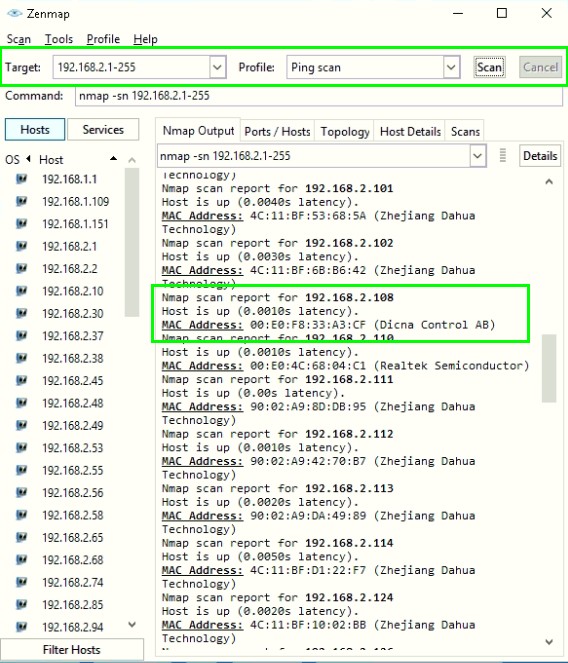
- The last method to locate a device on the network is to use NMap. This tool will scan the network, and locate and devices. Be sure to use, "Ping Scan" and input the range of IP addresses that you wish to search for into the tool. Example: 192.168.2.1-255 will scan all IP addresses starting at "192.168.2.1" to "192.168.2.255" and all IP addresses in between. You can also use this tool to determine which ports the device is broadcasting on currently.